Let’s say we have an Nginx virtual host like following
server {
listen 80;
root /var/www/html;
server_name serverok.in;
index index.htm index.html;
}
To make it SSL enabled, add the following to the server entry.
listen 443 ssl http2;
ssl_certificate /etc/ssl/serverok.crt;
ssl_certificate_key /etc/ssl/serverok.key;
ssl_client_certificate /etc/ssl/serverok.ca;
ssl_client_certificate introduced in Nginx version 1.19.4. If you are using an older version, add your ca-bundle after SSL certificate.
Example
server {
listen 80;
root /var/www/html;
server_name serverok.in;
index index.htm index.html;
listen 443 ssl http2;
ssl_certificate /etc/ssl/serverok.crt;
ssl_certificate_key /etc/ssl/serverok.key;
ssl_client_certificate /etc/ssl/serverok.ca;
location / {
try_files $uri/index.html $uri.html $uri;
}
}
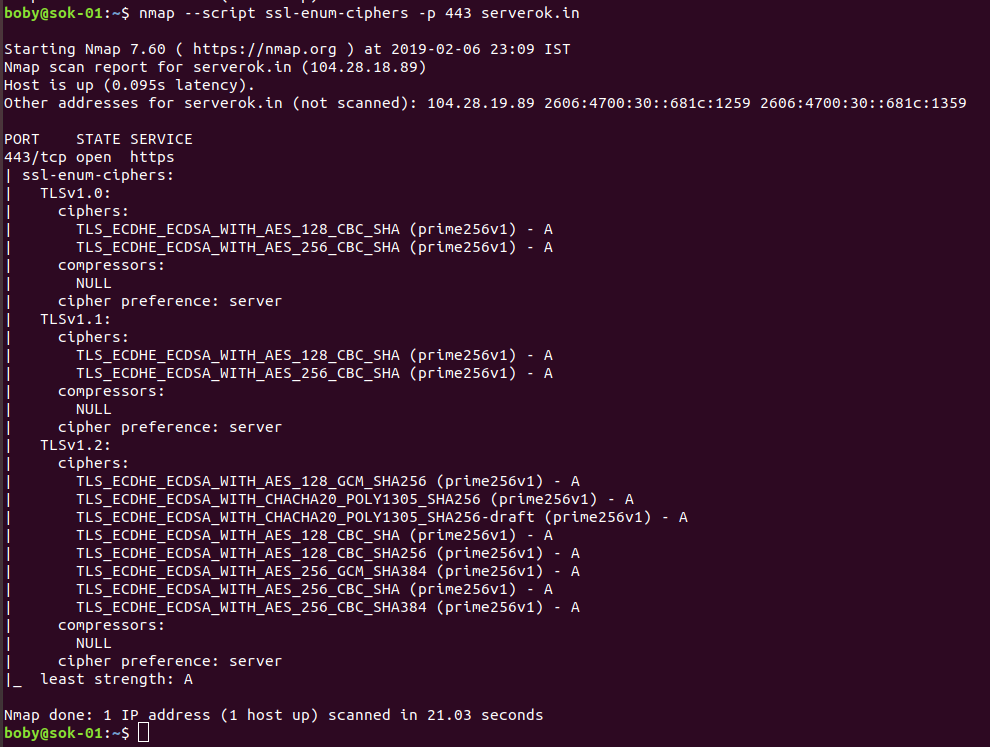
SSL protocols
ssl_session_cache shared:le_nginx_SSL:10m;
ssl_session_timeout 1440m;
ssl_session_tickets off;
ssl_protocols TLSv1.1 TLSv1.2;
ssl_prefer_server_ciphers on;
ssl_ciphers "ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:ECDHE-ECDSA-DES-CBC3-SHA:ECDHE-RSA-DES-CBC3-SHA:EDH-RSA-DES-CBC3-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA:!DSS";
dhparam
Create
openssl dhparam -out /etc/ssl/dhparam.pem 2048
In your nginx config, add
ssl_dhparam /etc/ssl/dhparam.pem;
Redirect Traffic to SSL
server {
listen 80;
server_name DOMAIN.TLD www.DOMAIN.TLD;
return 301 https://$host$request_uri;
}
If you don’t want to redirect SSL verification requests to HTTPS, use
server {
listen 80;
server_name DOMAIN_NAME;
location ~ ^/.well-known/ {
allow all;
autoindex on;
root /var/www/html;
}
location / {
return 301 https://$host$request_uri;
}
}
Disable TLSv1 in Nginx
Nginx Proxy SSL Verification
Nginx Redirect HTTP to HTTPS
See Nginx